Enabling Remote Desktop Services in a Windows Azure Virtual Machine with Active Directory Installed
•• Updated 7/30/2012 with added:
- Link to Windows Server Azure 2008 R2 Remote Desktop Services (5-User Client Access License), US$749.00 from the Microsoft Store
- “Fast Publish” note and publication date to Microsoft server software support for Windows Azure Virtual Machines below
- Link to Microsoft Volume Licensing Brief: Licensing Microsoft Server Products in Virtual Environments (*.docx)

Virtualized Desktop Services fall under the terms of the Windows Server Licensing Agreement. Unless you are an Independent Software Vendor (ISV) using SPLA[*] licensing to provide a SaaS based service, Windows Server does not include License Mobility to Public Clouds, and as a result Virtualized Desktop Services are not licensable on Windows Azure and other Public Clouds because of restrictions under the Windows Server License Agreement. Virtualized Desktop Services include Remote Desktop Services (RDS), Remote Terminal Services, and related third party offerings (example given - Citrix XenDesktop).
* Service Provider Licensing Agreement, see:
- Microsoft Volume Licensing: Licensing Options for Service Providers
- Licensing Benefits with the Microsoft Services Provider License Agreement (SPLA)
In addition, see Microsoft Support Services Article ID 2721672: Microsoft server software support for Windows Azure Virtual Machines, which contains the following lists:
Windows Server 2008 R2 and later versions are supported for the following roles:
- Active Directory Domain Services
- Active Directory Federation Services
- Active Directory Lightweight Directory Services
- Active Directory Rights Management Services
- Application Server
- DNS Server
- Fax Server
- Network Policy and Access Services
- Print and Document Services
- Web Server (IIS)
- Windows Deployment Services
- Windows Server Update Services
- File Services
The following features are not supported on Windows Azure Virtual Machines: BitLocker, Failover Clustering and Network Load Balancing.
•• Note This is a "FAST PUBLISH" article created directly from within the Microsoft support organization. The information contained herein is provided as-is in response to emerging issues. As a result of the speed in making it available, the materials may include typographical errors and may be revised at any time without notice. See Terms of Use for other considerations.
•• Article ID: 2721672 - Last Review: June 19, 2012 - Revision: 2.0
RDS and related services aren’t included in the supported list but aren’t listed as non-supported features.
I am investigating this issue and will update this post when I learn anything more.
Contents, Part I (Creating a Windows Azure Virtual Machine with a New Active Directory Forest for Remote Desktop Services):
- Create a Windows Azure Virtual Network and Affinity Group
- Create an Empty Cloud Service for the Virtual Machine
- Deploy a Virtual Machine in the Cloud Service
- Install Active Directory with DCPromo
Contents, Part II (this post):
TechNet’s Remote Desktop Services in Windows Server 2008 R2 page has links to the following topics:
- Product Evaluation
- Getting Started
- Planning and Architecture
- Deployment
- Operations
- Troubleshooting
- Technical Reference
You can learn more about RDS from TechNet’s Remote Desktop Services topic, which includes subtopics for:
- Remote Desktop Session Host (RD Session Host)
- Remote Desktop Virtualization Host
- Remote Desktop Session Host Configuration
- Remote Desktop Services Manager
- Remote Desktop Services User Properties
- RemoteApp Manager
- Remote Desktop Licensing Manager
- Remote Desktop Gateway Manager
- Remote Desktops
- Remote Desktop Connection Manager
Each RDS client must have an RDS Client Access License (CAL) installed within the 120-day licensing grace period. RDS CALs cost about $380 for a pack of five.
• Updated 7/8/2012 by splitting into two parts with new items marked •.
Install the Remote Desktop Services Role and Features
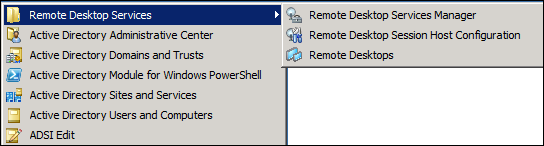
Although Windows Server 2008 R2’s Remote Desktop Services (RDS) menu contains Remote Desktop Services Manager, Remote Desktop Session Host Configuration and Remote Desktop items:
RDS roles aren’t installed by default. To install Windows Server 2008 R2 SP1’s RDS roles and features, do the following:
1. Launch Server manager from the Taskbar icon:
2. Click the Add Roles button to start the Add Roles Wizard, click Next to bypass the splash screen, and mark the Remote Desktop Services checkbox:
Note: You might want to install Application Server and Web Server (IIS) roles also at this point, but these roles are outside this post’s scope.
3. Click Next to open the Remote Desktop Services dialog, which includes a link to the local RDS help file:
4. Click Next and mark the Remote Desktop Session Host, Desktop Licensing, Connection Broker, Gateway and Web Access check boxes:
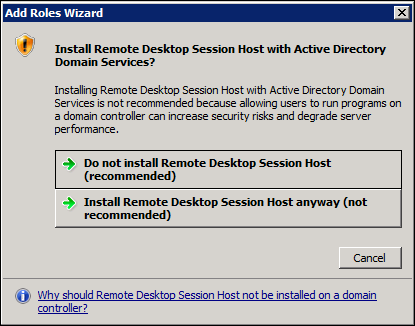
You receive the following warning message when you mark the Session Host check box:
4B. Click the Install Remote Desktop Session Host Anyway button to continue. Domain Controller performance isn’t likely to be an issue with a few users sharing this virtual machine.
The following dialog opens when you click the Remote Desktop Gateway check box:
4C. Click the Add Required Role Services to continue.
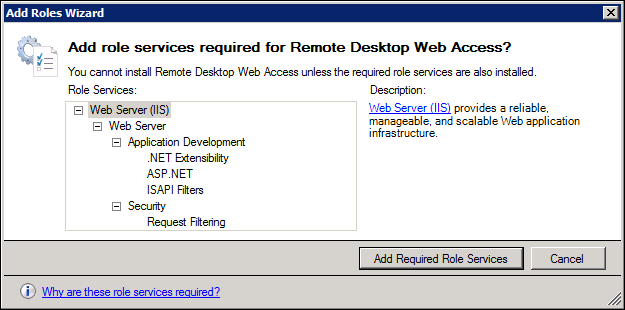
The following dialog opens when you click the Remote Desktop Web Access check box:
4D. Click the Add Required Role Services to continue.
5. Click Next to open the Uninstall and Reinstall Applications for Compatibility dialog, which isn’t applicable at this point because you haven’t installed any applications.
6. Click Next to open the Specify Authentication Method for Remote Desktop Session Host dialog. If all RDS clients will run Windows Vista or later (Windows 7 or 8), mark the Require Network Level Authentication option; to support earlier Windows versions, select the Do Not Require Network Level Authentication:
7. Click Next to open the Specify Licensing Mode dialog and accept the Configure Later option’s 120-day grace period for deciding on the licensing mode and obtaining Client Access Licenses (CALs):
8. Click Next to open the Select User[s or] Groups Allowed Access To This RD Session Host Server dialog, click the Add button to open the Select Users, Computers or Groups dialog and type the group names, starting with Domain Admins. If you’ve added application-specific user groups for RDS, add and check the group names.
9. Click OK to dismiss the Select Users, Computers or Groups dialog and click Next to open the Configure Client Experience. Unless the applications you plan to share have a compelling requirement for audio and video features or Windows Aero, don’t enable these features:
10. Click Next to open the Configure Discovery Scope for RD Licensing dialog. Accept Microsoft’s recommendation and don’t mark the Configure a Discovery Scope for This License Server check box:
11. Click Next to open the Choose a Server Authentication Certificate for SSL Encryption dialog and, if you don’t have a certificate from a CA for the domain (which is unlikely at this point), select the Choose a Certificate for SSL Encryption Later option:
Note: You’ll configure a self-signed certificate with the Gateway Manager in the next section.
12. Click Next to open the Create Authorization Policies for RD Gateway dialog and mark the Later option:
Note: You’ll configure a RD CAP and RD RAP with the Gateway Manager in the next section.
13. Click Next to read the Network Policy and Access Services dialog, click Next to open the Select Role Services dialog and accept the Network Policy Server default:
Note: Network Policy Services are required for Gateway Services.
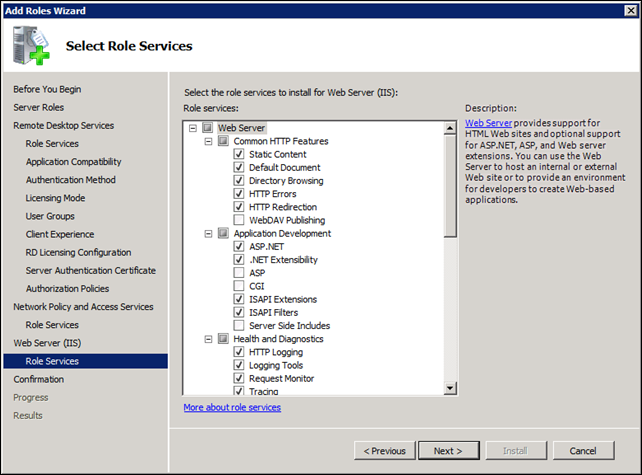
14. Click Next to read the Web Server (IIS) dialog, click Next again to open the Select Role Services for IIS dialog and accept the defaults:
15. Click Next to review the Confirm Installation Selections dialog:
16. Click Install to start the installation process, display the Installation Progress dialog for a minute or two and finally display the Installation Results dialog:
• 17. Click Close and Yes to restart the server, complete the installation and display the Installation Results dialog (shown here after an overnight hiatus):
Note: Links in the warning messages point to Remote Desktop Licensing Manager, RemoteApp Manager or Remote Desktop Session Host Configuration help files which you can access through the Help menu item of their respective Microsoft Management Console (MMC) snap-ins (see the following section.)
• 18. Review the messages, click the Print, E-mail, or Save the Installation Report link to open the report in IE and save it to a Installation Report.mht (or .html) file.
Following is the full text of the four warning and two informational messages from the saved Installation Report.mht file;
- This license server is not registered as a service connection point (SCP) in Active Directory Domain Services (AD DS). The license server will not appear in the list of known license servers in the Remote Desktop Session Host Configuration tool. To register the license server as an SCP in AD DS, use Review Configuration in the Remote Desktop Licensing Manager tool.
- RD Web Access requires additional configuration. On the Configuration page of the RD Web Access Web site, you need to specify the source that will provide the RemoteApp programs and desktops that will be displayed to users. For more information, see Configuring the RD Web Access Server.
- Ensure that your RD Session Host servers are correctly configured to use this license server. For more information, see Configure License Settings on an RD Session Host Server.
- Use the Remote Desktop Session Host Configuration tool to specify a Remote Desktop license server for this RD Session Host server to use. For more information, see Configure License Settings for an RD Session Host Server.
Note: See the “Remote Desktop Licensing Manager Snap-in” subsection below to confirm that the license server is registered as an SCP in Active Directory.
RD Connection Broker requires additional configuration, depending on why RD Connection Broker is being deployed:
- Create a load-balanced RD Session Host server farm by using RD Connection Broker.
- Configure RD Connection Broker to deploy RemoteApp and Desktop Connection.
Default RD Web Access site: https://OAKLEAF-VM2/RDWeb
• 19. Click Close to dismiss the Wizard and restart the VM to complete installation of all roles and features.
• Configure Remote Desktop Services
After installing RDS, the Start, Administrative Tools, Remote Desktop Services menu appears as follows:
The following sections start with screen captures of the MMC snap-in for each feature to be configured in its state before configuration. Steps required to configure the feature follow.
Configure the Remote Desktop Gateway Manager
A certificate and connection and resource authorization policies are required for the Gateway Server serve clients.
To create a self-signed certificate, which is adequate for testing RDS features, for the Remote Desktop Gateway server, do the following:
1. On the RD Gateway server, open Remote Desktop Gateway Manager. To open Remote Desktop Gateway Manager, click Start, point to Administrative Tools, point to Remote Desktop Services, and then click Remote Desktop Gateway Manager.
2. In the Remote Desktop Gateway Manager console tree, right-click the local RD Gateway Server node, which is named for the computer on which the RD Gateway server is running, and then click Properties.
3. In the results pane, under Configuration Status, click View or modify certificate properties.
4. On the SSL Certificate tab, click the Create a Self-Signed Certificate option, and then click the Create and Import Certificate button.
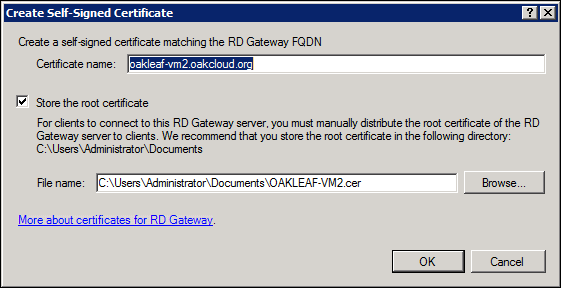
5. In the Create Self-Signed Certificate dialog, do the following:
5A. In the Certificate name box, verify that the correct fully qualified domain name (FQDN) is specified for the self-signed certificate, or specify a new name. The FQDN must match the DNS name that the client uses to connect to the RD Gateway server, unless you are using wildcard certificates or the SAN attributes of certificates.
5B. To store the root certificate in a specified location so that you can manually distribute the root certificate to clients, verify that the Store the root certificate check box is selected, and then specify where to store the certificate. By default, this check box is selected and the certificate is stored under the %Windir%\Users\Username\Documents folder.
5C. Click OK to close the dialog.
6. If you selected the Store the root certificate check box and specified a location for the certificate, a message will appear stating that RD Gateway has successfully created the self-signed certificate, and confirming the location of the stored certificate. Click OK to close the message.
7. Click OK again to close the RD Gateway Server Properties dialog.
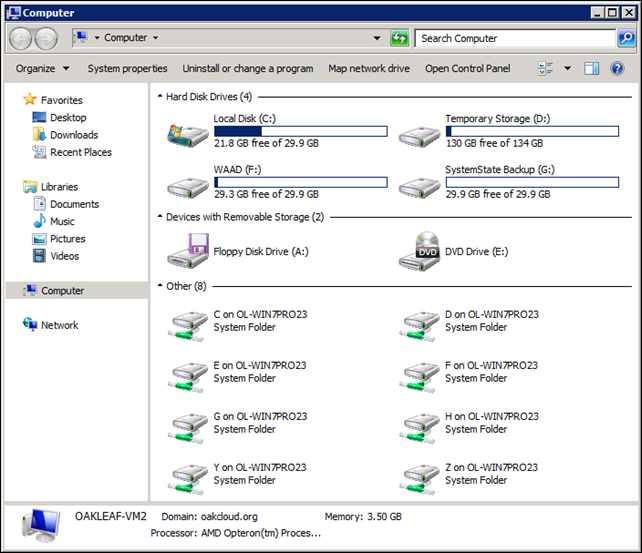
8. Choose Start, Computer to open the Computer window, which includes links to disk drives (System Folders) on your client computer, OL-WINPRO23 for this example:
9. Copy the certificate file, OAKLEAF-VM2.cer for this example, from C:\Users\Administrator\My Documents on OakLeaf-VM2 to a C:\Users\YourUserName\My Documents\Certificates folder on your computer.
Note: You must provide a copy of the certificate to each client connecting to RDS for importing to their certificate store in order to designate OakLeaf-VM2 as a Trusted Root Certification Authority for the SSL connection.
At this point, the Remote Desktop Gateway Manager Snap-in appears as follows:
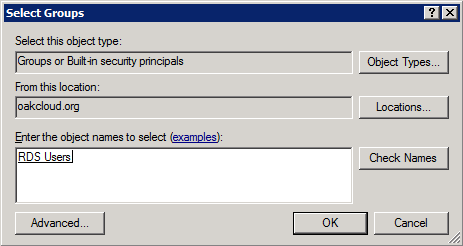
To create a new RDS Users group and add a new user to the group in preparation for creating an RD Connection Authorization Policy (CAP), do the following:
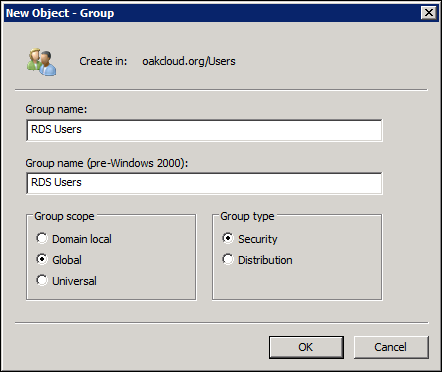
1. Choose Start | Administrative Tools | Active Directory Users and Computers, right-click the Users node and choose New | Group to open the New Object - Group dialog:
2. In the New Object - Group dialog, type the name of the group, RDS Users for this example and accept the default Global option:
Note: The Group Scope must be Global or Universal to enable the group to be added to the local Remote Desktop Users group in the later “Configuring the Remote Desktop Connection Manager” section.
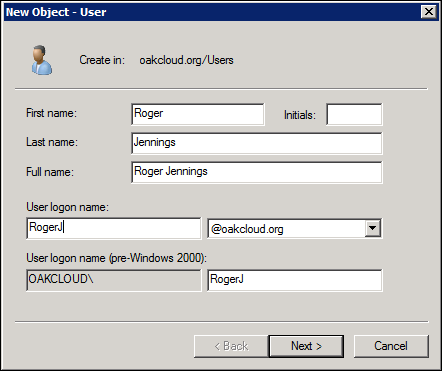
3. Click OK to create the group, then right-click the Users node again, choose New, User to open the New Object - User dialog, type your name, and assign a Logon name:
4. Click Next, type and confirm a strong password, clear the User Must Change Password at Next Login check box and mark the Password Never Expires check box:
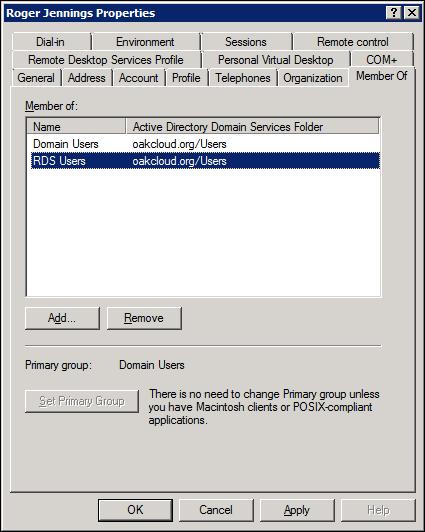
5. Click Next and Finish to add the new user, double-click the new user’s item in the list to open the Properties sheet and click the Member Of tab:
6. Click the Add button to open the Select Groups dialog, type RDS Users in the text box, and click the Check Names button to verify the group name:
7. Click OK to close the dialog and add the new user to the RDS Users group:
8. Click OK to close the Properties sheet.
9. Double click the Administrator user item in the list and repeat steps 5 through 8 to add the Administrator account to the RDS Users group.
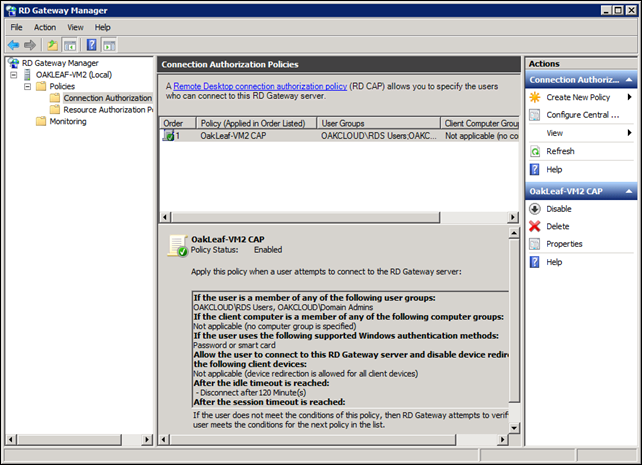
To create a new CAP for RDS Users, do the following:
1. In the RD Gateway Manager Configuration Status region click the Create Connection Authorization Policy arrow to open the RD CAP dialog.
2. In the New RD CAP dialog, on the General tab, in the Policy name box, type a name for the policy, OakLeaf-VM2 CAP for this example, and then verify that the Enable this policy check box is selected:
4. On the Requirements tab, under Supported Windows authentication methods, select one or both of the following check boxes:
- Password
- Smart card
When both of these options are selected, clients that use either authentication method are allowed to connect.
5. Under User group membership (required), click Add Group, and then specify user groups whose members can connect to the RD Gateway server. You must specify at least one user group.
6. In the Select Groups dialog, specify the user group location and name, and then click OK as needed to check the name and to close the Select Groups dialog box. To specify more than one user group, do either of the following:
- Type the name of each user group, separating the name of each group with a semi-colon or
- Add additional groups from different domains by repeating this step for each group.
7. To specify optional additional computer domain membership criteria that client computers must meet, on the Requirements tab, under Client computer group membership (optional), click Add Group, and then specify the computer groups.
8. Click OK to close the dialog and enable the groups’ members.
9. To specify the computer groups, you can use the same steps that you used to specify user groups.
10. On the Device Redirection tab, select one of the following options to enable or disable redirection for remote client devices:
- To permit all client devices to be redirected when connecting through the RD Gateway server, click Enable device redirection for all client devices. By default, this option is selected.
- To disable device redirection for only certain device types when connecting through the RD Gateway server, click Disable device redirection for the following client device types, and then select the check boxes that correspond to the client device types for which device redirection should be disabled.
11. To only allow client connection to servers that enforce secure device redirection, on the Device Redirection tab, click Only allow client connections to Remote Desktop Session Host servers that enforce RD Gateway device redirection.
Caution: Selecting Only allow client connections to Remote Desktop Session Host servers that enforce RD Gateway device redirection will prevent users that are running versions older than Remote Desktop Connection (RDC) 7.0 from connecting.
12. On the Timeouts tab, select the following options to enable or disable timeouts:
- To set disconnection timeout settings for an idle remote session when connecting through the RD Gateway server, select the Enable idle timeout check box. In the Disconnect session after idle for box, enter the time, in minutes, to set the maximum time that a remote session can be idle before the session is disconnected.
- To set session timeout settings for a remote session when connecting through the RD Gateway server, select the Enable session timeout check box. In the Time out session after box, enter the time, in minutes, to set the time for session timeout to take effect. Select the action to take after the user session timeout is reached:
- To disconnect the remote session, click Disconnect session.
- To have the session continue uninterrupted, unless changes to the user profile have been made, click Silently re-authenticate and reauthorize session.
13. Click OK to apply your settings.
The new local RD CAP that you created appears in the Remote Desktop Gateway Manager results pane. When you click the name of the RD CAP, the policy details appear in the lower pane.
14. Select the Resource Authorization Policies item in the navigation pane, click Create New policy in the Actions pane, and choose Custom to open the New RD RAP dialog.
15. Type a name for the RAP, Oakleaf-VM2 RAP for this example, and an optional description in the General tab’s text boxes:
16. Click the User Groups tab and add the RDS Users and Domain Admins groups as you did for the new CAP in steps 5 and 6:
17. Click the Network Resource Tab, accept the default Active Directory Domain Services option, click the Add button, type Domain Controllers in the Select Groups dialog’s text box, and click OK to add it:
18. Click the Allowed Ports tab, accept the default port 3389, and click OK to add the new RAP:
Add Remote Apps with the RemoteApp Manager
1. Choose Start, Administrative Tools, Remote Desktop Services, RemoteApp Manager to open its MMC snap-in:
Note: It isn’t necessary to add the domain controller to the TS Web Access Computers group because it is same computer that is the RemoteApps server.
2. Click the Digital Signature Settings Change button to open the RemoteApp Deployment Settings dialog and click the Sign with a Digital Certificate check box to enable the Change button:
3. Click the Change button to display a list of the certificates installed on the domain controller. If you have more than one certificate, select the one with the same name and validity dates that you created for the SSL protocol in steps 1 though 9 of the earlier “Configure the Remote Desktop Gateway Manager” section.
Tip: To check the validity dates of the SSL certificate, double click the certificate you saved in the Documents folder to open it. To disambiguate certificates with the same date, open the certificates’ properties sheets and compare the thumbprint values.
4. Click OK to accept the self-signed certificate:
5. Click OK to close the RemoteApp Deployment Settings dialog.
6. Click the A Remote Desktop Connection for This Server Is Not Visible in RD Web Access Change link to open the RemoteApp Deployment Settings dialog with the RD Session Host Server tab active and mark the Show a Remote Desktop Connection … check box:
7. Click OK to close the RemoteApp Deployment Settings dialog.
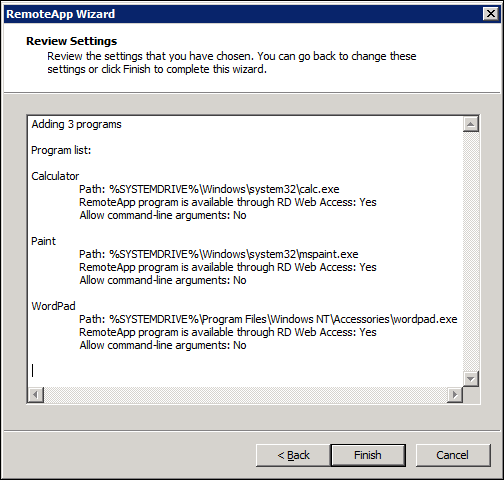
8. Click the Add RemoteApp Programs link in the Actions pane to open the RemoteApp Wizard, click Next to open the Choose Programs … dialog and select a few sample programs, such as Calculator, Paint and WordPad:
Tip: After you install third party programs with appropriate licenses, click Browse to add their *.exe files to the list.
9. Click Next to confirm your selections in the Review Settings dialog:
10. Click Finish to add the selected applications to RemoteApp Manager’s list:
11. Close RemoteApp Manager.
Configuring the Remote Desktop Connection Manager:
This tutorial doesn’t cover providing Personal Virtual Desktops or Virtual Desktop pools. Following is the Remote Desktop Connection checklist for providing RemoteApps only:
- Install and configure a RemoteApp source.
- Install and configure an RD Connection Broker server.
- Install and configure an RD Web Access server.
- Make RemoteApp programs from a RemoteApp source available to users.
- Specify the name that users see to identify RemoteApp and Desktop Connection.
- Specify the RD Web Access servers through which RemoteApp and Desktop Connection is made available to users.
- Create a RemoteApp and Desktop Connection configuration file to distribute to users. (Optional)
Configure a Remote Desktop Session Host Server to Host RemoteApp Programs
1. To add groups or users to the Remote Desktop Users account, choose Start, Run and type control system in the Open text box:
2. Click OK to open the Control Panel\System and Security\System dialog:
3. Click the Remote Settings button to open the System Properties sheet with the Remote tab selected:
4. Click the Select Users button to open the Remote Desktop Users dialog, which includes the Domain Admins group by default:
Note: Disregard the advice to “go to Control Panel and open User Accounts.” These are local, not domain, groups and accounts.
5. Click Add to open the Add Users or Groups dialog, type RDS Users in the text box and click Check Names:
6. Click OK to close the dialog and return to the Remote Desktop Users dialog:
7. Click OK twice to return to the Control Panel\System and Security\System dialog and close that dialog.
8. To configure the TS Web Access Computers group, click Start, Administrative Tools, Active Directory Users and Computers to open the snap-in and select Users in the navigation pane.
9. In the right pane, double-click TS Web Access Computers to open the group’s Properties sheet, click Members, and click Add.
10. In the Select Users, Computers, Service Accounts, or Groups dialog, click Object Types.
11. In the Object Types dialog box, mark the Computers check box:
12. Click OK and In the Enter the object names to select box, type the computer name, oakleaf-vm2 for this example, and click Verify Names:
13. Click OK to close the Select … dialog:
14. Click OK to close the Properties sheet.
15. To add a RemoteApp Source for RemoteApp and Desktop connections, return to the Remote Desktop Connection Manager snap-in and, in the navigation pane, click RemoteApp Sources, on the Action menu, click Add RemoteApp Source, and type the computer name in the text box:
16. Click Add to add the server to the RemoteApp Source Name list:
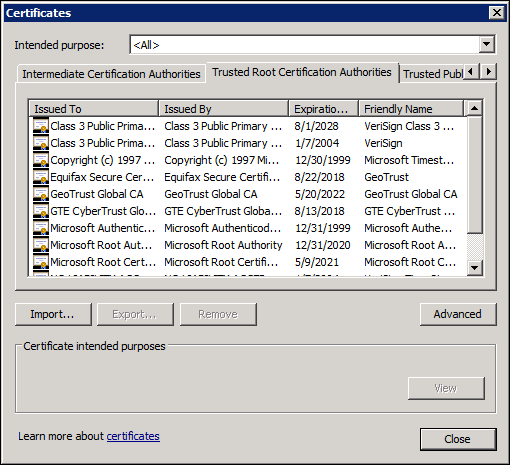
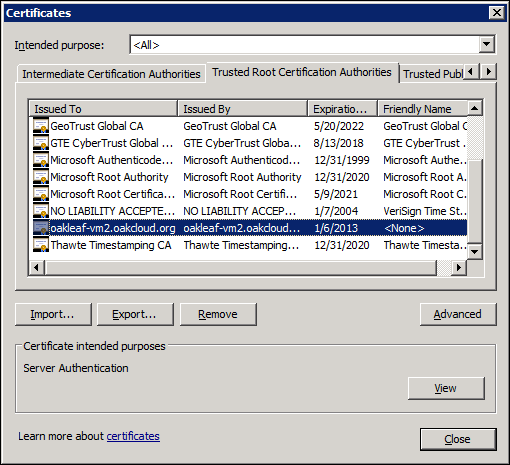
17. To trust the self-signed certificate you created earlier before configuring the Remote Desktop Services default configuration, open IE 9, click the Tools icon, click Internet options to open the Internet Options dialog and click the Content tab:
18. Click the Certificates tab to open the Certificates dialog and click the Trusted Root Certificates tab:
19. Click the Import button to launch the Certificate Import Wizard, click next, click the Browse button, navigate to the Documents folder in which you stored the ComputerName.cer certificate copy file, and double-click it to add its fully-qualified pat to the text box:
20. Click Next to accept the Trusted Root Certificates store and Next again to display this warning:
21. Click Yes to install the certificate and click OK to dismiss the Successful message:
22. Click the Trusted Publishers tab and repeat steps 19 through 21 to import the certificate for code signing:
23. Click Close to close the Certificates dialog and OK to close the Internet Options dialog.
24. Click Start, Administrative Tools, Remote Desktop Services, Remote Desktop Web Access Configuration to start Internet Explorer, click Continue to This Site when prompted, type your Administrator password in the Password text box, and select the This Is a Private Computer option:
Note: IE didn’t accept the certificate because the Web page’s address is localhost, rather than oakleaf-vm2waad.cloudapp.net.
25. Click Sign In to open the Configuration page and type the FQDN of the server, oakleaf-vm2.oakcloud.org:
26. Click OK to confirm the source name by displaying the RemoteApps you selected in step 8 of the preceding section:
27. Click the Calculator icon to open the RemoteApp dialog and mark the Don’t Ask Me Again … check box:
28. Click Connect to run Calculator on the Remote Desktop:
29. Click the Remote Desktop button, type the computer name in the Connect To text box, click the Options button to display other choices and select the bandwidth of your Internet connection in the performance list:
30. Click Connect to test the Remote Desktop connection:
Note: This warning message has no Don’t Ask Me Again … check box.
31. Click Connect to open the Windows Security dialog, type your password and mark the Remember My Credential check box:
32. Click OK to attempt the connection. You receive an Access Is Denied message from Windows Server 2008 R2, probably because you are already logged in with this account.
33. Close IE and return to the Remote Desktop Connection Manager, click the topmost item in the navigation pane, and click Refresh in the Actions pane to display the current state of the RD Connection Broker:
Remote Desktop Session Host Configuration Snap-in:
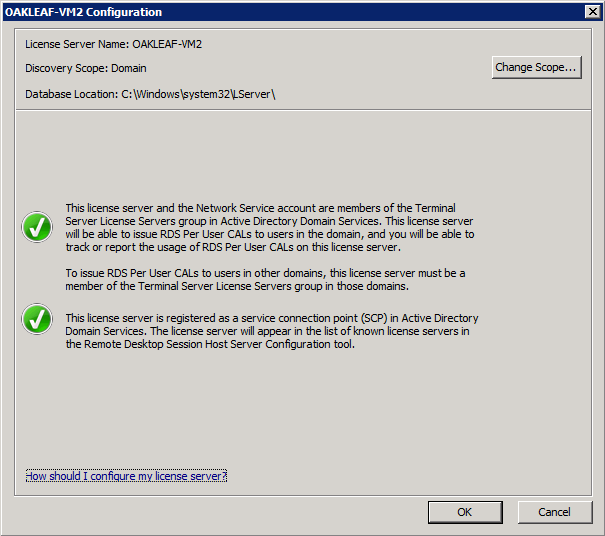
Remote Desktop Licensing Manager Snap-in
The service is deactivated, as indicated by the X in the red circle.
Choosing Action | Confirm Configuration displays the following message, indicating that the License Server is registered as an SCP in Active Directory:















![image_thumb[2] image_thumb[2]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEiQWlkVbFb6509QJy20-gGElKvRo0ciY1SnWew0xHsifcBUGLUe8aunRVsVHro4IEe-uyPFgWLI3Sr3YsKWAgEsdxfN5Zq64l4KrHklDSJUZGHInwf7FSv0t_tO799IthDchC_ELiBX/?imgmax=800)






































































0 comments:
Post a Comment