Windows Azure Mobile Services Preview Walkthrough–Part 6: Authentication with Third-Party Identity Providers
Scott Guthrie (@scottgu) announced the addition of Facebook, Google and Twitter as third-party OAuth identity providers for Windows Azure Mobile Services (WAMS) in his Windows Azure Mobile Services: New support for iOS apps, Facebook/Twitter/Google identity, Emails, SMS, Blobs, Service Bus and more post of 10/16/2012:
Our initial preview of Mobile Services supported the ability to authenticate users of mobile apps using Microsoft Accounts (formerly called Windows Live ID accounts). This week we are adding the ability to also authenticate users using Facebook, Twitter, and Google credentials. These are now supported with both Windows 8 apps as well as iOS apps (and a single app can support multiple forms of identity simultaneously – so you can offer your users a choice of how to login).
The below tutorials walk through how to register your Mobile Service with an identity provider:
- How to register your app with Microsoft Account
- How to register your app with Facebook
- How to register your app with Twitter
- How to register your app with Google
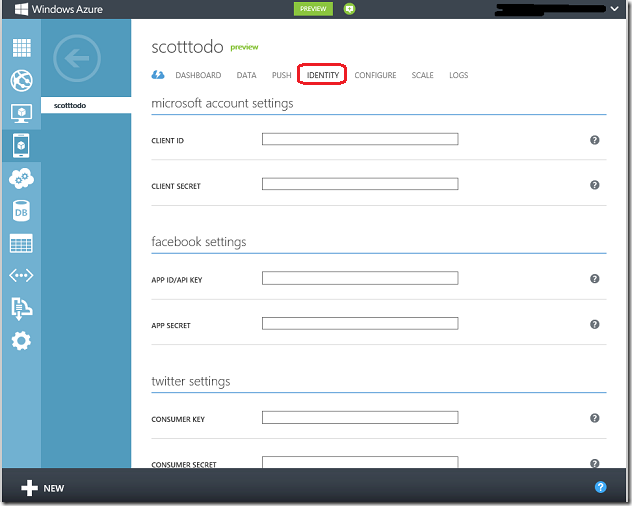
The tutorials above walk through how to obtain a client ID and a secret key from the identity provider. You can then click on the “Identity” tab of your Mobile Service (within the Windows Azure Portal) and save these values to enable server-side authentication with your Mobile Service:
You can then write code within your client or mobile app to authenticate your users to the Mobile Service. For example, below is the code you would write to have them login to the Mobile Service using their Facebook credentials:
Windows Store App (using C#):
var user = await App.MobileService
.LoginAsync(MobileServiceAuthenticationProvider.Facebook);
iOS app (using Objective C):
UINavigationController *controller =
[self.todoService.client
loginViewControllerWithProvider:@"facebook"
completion:^(MSUser *user, NSError *error) {
//...
}];
Learn more about authenticating Mobile Services using Microsoft Account, Facebook, Twitter, and Google from these tutorials:
Stay tuned for the complete tutorial (coming soon.)


















0 comments:
Post a Comment