Windows Azure and Cloud Computing Posts for 8/19/2013+
Top Stories This Week:
- Brad Anderson (@InTheCloudMSFT) described What’s New in 2012 R2: Enabling Modern Apps with the Windows Azure Pack in the Windows Azure Pack, Hosting, Hyper-V and Private/Hybrid Clouds section below.
- Guarav Mantri (@gmantri) described Consuming Windows Azure Service Management API In Java in the Windows Azure Virtual Machines, Virtual Networks, Web Sites, Connect, RDP and CDN section below.
| A compendium of Windows Azure, Service Bus, BizTalk Services, Access Control, Caching, SQL Azure Database, and other cloud-computing articles. |
Note: This post is updated weekly or more frequently, depending on the availability of new articles in the following sections:
- Windows Azure Blob, Drive, Table, Queue, HDInsight and Media Services
- Windows Azure SQL Database, Federations and Reporting, Mobile Services
- Windows Azure Marketplace DataMarket, Power BI, Big Data and OData
- Windows Azure Service Bus, BizTalk Services and Workflow
- Windows Azure Access Control, Active Directory, and Identity
- Windows Azure Virtual Machines, Virtual Networks, Web Sites, Connect, RDP and CDN
- Windows Azure Cloud Services, Caching, APIs, Tools and Test Harnesses
- Windows Azure Infrastructure and DevOps
- Windows Azure Pack, Hosting, Hyper-V and Private/Hybrid Clouds
- Visual Studio LightSwitch and Entity Framework v4+
- Cloud Security, Compliance and Governance
- Cloud Computing Events
- Other Cloud Computing Platforms and Services
Windows Azure Blob, Drive, Table, Queue, HDInsight and Media Services
<Return to section navigation list>
No significant articles so far this week.

<Return to section navigation list>
Windows Azure SQL Database, Federations and Reporting, Mobile Services
No significant articles so far this week.
<Return to section navigation list>
Windows Azure Marketplace DataMarket, Cloud Numerics, Big Data and OData
No significant articles so far this week.
<Return to section navigation list>
Windows Azure Service Bus, BizTalk Services and Workflow
See Brad Anderson’s (@InTheCloudMSFT) description of What’s New in 2012 R2: Enabling Modern Apps with the Windows Azure Pack of 8/21/2013 in the Windows Azure Pack, Hosting, Hyper-V and Private/Hybrid Clouds section below.
No significant articles so far this week.
<Return to section navigation list>
Windows Azure Access Control, Active Directory, Identity and Workflow
No significant articles so far this week.
<Return to section navigation list>
Windows Azure Virtual Machines, Virtual Networks, Web Sites, Connect, RDP and CDN
Guarav Mantri (@gmantri) explained Consuming Windows Azure Service Management API In Java in an 8/25/2013 post, which begins:
I have written some blog posts about consuming Windows Azure Service Management API using C#. I have been quite active on StackOverflow trying to answer some questions about Windows Azure. Recently I observed a number of questions there asking for consuming this API through Java. Also somebody approached me asking for something like this. This blog post is a result of that. In this post, I will talk about how one can consume this API using Java.
Its been ages that I have worked with Java so things I describe below may sound trivial to experienced Java developers so please bear with me. Also if there’re better ways to do things, please let me know as most of the code you will see below would be the result of massive Internet searches.
About Windows Azure Service Management API
Let’s take a moment to talk briefly about what this API is and some other fundamental things about it and then we’ll get into the code.
What?
Windows Azure Service Management API is a REST based API for managing Windows Azure resources. Using this API, you can manage your cloud services, storage accounts, virtual machines, virtual networks and lot more. Essentially the things you could do on Windows Azure Portal can be done through this API. In fact, Windows Azure Portal is built on top of this API. You can learn more about this here: http://msdn.microsoft.com/en-us/library/windowsazure/ee460799.aspx.
How it Works?
To use this API, you would need 2 things:
- Subscription Id: This is a GUID which uniquely identifies your subscription. You can get this information through portal.
- Management Certificate: A management certificate is required to authenticate your API calls. This management certificate must be associated with your subscription which you can do by upload the certificate in the portal. You could either create a management certificate on your own and associate it with your subscription (this is covered in details in this post) or you could ask Windows Azure platform to create a management certificate for you and associate it with your subscription. This is done through a process called “Download Publish Profile File”. I have written a blog post about it some days back which you can read here: http://gauravmantri.com/2012/09/14/about-windows-azure-publish-settings-file-and-how-to-create-your-own-publish-settings-file/.
Since the API is a REST based API, the endpoints are accessible over HTTP. In your code, you create an endpoint specific to a particular kind of operation you want to perform. Then you create an HTTP request for that endpoint. To authenticate the request, you attach the management certificate along with that request. You can learn more about the authentication here: http://msdn.microsoft.com/en-us/library/windowsazure/ee460782.aspx.
Now that we know a bit about the API, let’s look at how we can consume this API using Java.
Using Publish Profile File
I will not go into details about consuming this API using the publish profile file as it is covered extremely well by Andy Cross and Richard Conway in their Elastacloud blog post: http://blog.elastacloud.com/2012/09/29/a-windows-azure-service-management-client-in-java/. If this is something you’re looking for, stop reading this post and head over to their website otherwise read on. …
Gaurav continues with the details of his backup plug-in and biographies of the interns who implemented it.
<Return to section navigation list>
Windows Azure Cloud Services, Caching, APIs, Tools and Test Harnesses
No significant articles so far this week.
Return to section navigation list>
Windows Azure Infrastructure and DevOps
Barbara Darrow (@gigabarb) asserted “Microsoft under Ballmer has poured billion after billion into Windows Azure which is now, by all accounts a pretty impressive, massively scaled cloud. Now is not the time to retrench.” in a deck for her Hey! New Microsoft CEO, whoever you are, take care of Azure; The week in cloud article of 8/25/2013 for GigaOm’s Cloud blog:
The news Friday, mercifully early in the day, was that Microsoft CEO Ballmer is transitioning out of that role in a process that could take a year. But hopefully, it will take much less than that, given the distraction an executive search of that magnitude will mean.
There’s no shortage of speculation — about who will get the nod — some even speculate that the head of the search committee, former Symantec CEO and Microsoft director John Thompson might act as interim CEO. But one thing the new top dog is should do is make sure the build out of Windows Azure continues apace. And not, watch out.
For all Microsoft’s woes — the mis-steps in phones and tablets which led to a mind-boggling $900 million write-down last quarter, the 2007 Vista debacle that Ballmer conceded was his biggest regret, don’t forget that Microsoft is one of a handful of companies with the resources — in cash and in talent — to build a truly massive and scalable infrastructure. Microsoft profit last quarter, was $5 billion compared to $3.2 billion for Google and $6.9 billion for Apple according to The New York Times.
And, for the last full fiscal year ending June 30, it logged profit of nearly $22 billion on revenue of $78 billion and averaged $150,000 in sales every minute, the Wall Street Journal pointed out
Chew on that for a minute.
Microsoft’s problem is that the market it dominates — is a market in decline. The problem is that while Windows still owns the market share lead on traditional PCs, it runs just 15 percent of all devices including PCs, smartphones and tablets, according to Gartner.
So here’s the deal, reviews of Windows Azure (finally) are good. Microsoft is one of maybe 3 or 4 companies that can give Amazon Web Services and Google a run for their money in brute cloud infrastructure. And what do next-gen mobile applications and games need to run well? Massive infrastructure.
it still makes some of the biggest money-gushers in the technology business, including its Windows operating system for personal computers and Office applications like Word. Its profit last quarter was nearly $5 billion, compared with $3.2 billion for Google and $6.9 billion for Apple.
The Windows Azure Team’s graphics arts group posted a series of Windows Azure Infographics on 8/21/2013:
These technical posters and infographics are excellent for learning and training. Zoom into details, download, or print (26X30"/66.04X99.06cm). Most of these posters and all future posters will link to deeper technical content through the mobile tags for a more complete set of information.
<Return to section navigation list>
Windows Azure Pack, Hosting, Hyper-V and Private/Hybrid Clouds
Brad Anderson (@InTheCloudMSFT) continued his Enable Modern Business Apps TechNet series with What’s New in 2012 R2: Enabling Modern Apps with the Windows Azure Pack on 8/21/2013:
Don’t let the title fool you – this post is critically important for Developers and IT pros.
The reason I call out this warning up front is that often, when I’m speaking at conferences around the world, as soon as I start to discuss the developer perspective and developer tools, many IT Pros in the room starts playing Angry Birds while they wait for the developer section to be over.
Why is it so important for IT Pros to understand how modern applications are built? The answer is simple: IT Pros are the ones who build and operate the infrastructure that hosts these applications, and, the more you know about how these applications are built, the better you will understand their platform requirements.
That’s the tactical reason. There is also a strategic reason.
If your organization is not already in the process of defining it’s cloud strategy – it soon will be. You need to be a contributor and leader in these conversations. By mastering today’s topics, you can become a part of the conversation and define the long-term solution, rather than someone who is simply reacting to decisions they were not a part of making.
The future of the IT Pro role will require you to know how applications are built for the cloud, as well as the cloud infrastructures where these apps operate, is something every IT Pro needs in order to be a voice in the meetings that will define an organization’s cloud strategy. IT pros are also going to need to know how their team fits in this cloud-centric model, as well as how to proactively drive these discussions.
These R2 posts will get you what you need, and this “Enable Modern Business Apps” pillar will be particularly helpful.
Throughout the posts in this series we have spoken about the importance of consistency across private, hosted and public clouds, and we’ve examined how Microsoft is unique in its vision and execution of delivering consistent clouds. The Windows Azure Pack is a wonderful example of Microsoft innovating in the public cloud and then bringing the benefits of that innovation to your datacenter.
The Windows Azure Pack is – literally speaking – a set of capabilities that we have battle-hardened and proven in our public cloud. These capabilities are now made available for you to enhance your cloud and ensure that “consistency across clouds” that we believe is so important.
A major benefit of the Windows Azure Pack is the ability to build an application once and then deploy and operate it in any Microsoft Cloud – private, hosted or public.
This kind of flexibility means that you can build an application, initially deploy it in your private cloud, and then, if you want to move that app to a Service Provider or Azure in the future, you can do it without having to modify the application. Making tasks like this simple is a major part of our promise around cloud consistency, and it is something only Microsoft (not VMware, not AWS) can deliver.
This ability to migrate an app between these environments means that your apps and your data are never locked in to a single cloud. This allows you to easily adjust as your organization’s needs, regulatory requirements, or any operational conditions change.
A big part of this consistency and connection is the Windows Azure Service Bus which will be a major focus of today’s post.
The Windows Azure Service Bus has been a big part of Windows Azure since 2010. I don’t want to overstate this, but Service Bus has been battle-hardened in Azure for more than 3 years, and now we are delivering it to you to run in your datacenters. To give you a quick idea of how critical Service Bus is for Microsoft, consider this: Service Bus is used in all the billing for Windows Azure, and it is responsible for gathering and posting all the scoring and achievement data to the Halo 4 leaderboards (now that is really, really important – just ask my sons!). It goes without saying that the people in charge of Azure billing and the hardcore gamers are not going to tolerate any latency or downtime getting to their data.
With today’s topic, take the time to really appreciate the app development and app platform functionality in this R2 wave. I think you’ll be really excited about how you can plug into this process and lead your organization.
This post, written by Bradley Bartz, a Principal Program Manager from Windows Azure, will get deep into these new features and the amazing scenarios that the Windows Azure Pack and Windows Azure Service Bus enable. As always in this 2012 R2 series, check out the “Next Steps” at the bottom of this for links to additional information about the topics covered in this post.
* * *
When building modern applications, developers want a way to connect multiple tiers of their application as well as a way to consume services offered by third party vendors. Different tiers within modern applications may have different hosting methods, e.g. front-tier components are often written as web applications, while back-end services may be hosted in a virtual machine.
The Windows Server 2012 R2 platform offers multiple hosting alternatives, but there is still a need to enable connectivity between an application’s components and services. One of the common approaches is to exchange messaging using a broker.
Two years ago, we have introduced the Windows Azure Service Bus which provides messaging capabilities in the public cloud. Since its launch we’ve seen multiple scenarios where messaging has been a valuable in addition to the basic back-end/front-end pattern. We’ve seen messaging used to connect clients and devices to a cloud service, as well as scenarios where messaging was used for integration.
Just a year ago we released Service Bus for Windows Server v1.0, which enables a developer to build, test, and run loosely-coupled, message-driven applications in self-managed environments as well as on developer computers.
Now, with the release of Windows Server 2012 R2 (just one year after we released Service Bus 1.0 for Windows Server and introduced the runtime capabilities of brokered messaging on-premises!), we are proud to release the second version of our broker called Service Bus 1.1 for Windows Server.
In this release we have invested in an integrated experience as a part of the Windows Azure Pack, with the goal of bringing a self-service tenant experience that is consistent with the one that currently exists in Windows Azure.
We’ve listened closely to our customers and focused on improving the following 3 core scenarios with the Service Bus 1.1 for Windows Server and the Windows Azure Pack:
- Application Messaging Patterns with Service Bus
With Service Bus we support basic as well as advanced messaging patterns for use in modern applications. With this release we’ve also added new messaging capabilities, additional protocols, and simplified APIs to enable developers to write better applications faster.- Manage Messaging entities across clouds
Whether you’re developing for the public cloud, private cloud, or a hosted cloud (with your service provider), developers will be able to write applications once and then use it anywhere within these clouds – without needing to recompile. This can be done by simply changing an entry in the configuration file.- Offering Alternatives with Service Bus
Whether you are an Independent Software Vendor developing software and services for others, an enterprise which deploys home-grown applications, or a developer looking for an easy to deploy messaging component, you can use Service Bus in your topology. With this release we’ve improved the hosting capabilities for enterprises and service providers enabling new hosting topologies. …
Brad continues with the following among the major topics:
Scenario 1: Application Messaging Patterns with Service Bus.
Messaging with Service Bus: Building Loosely Coupled Application
Messaging with Service Bus: Publish-Subscribe Patterns
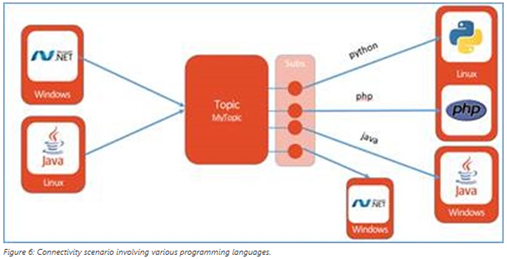
Messaging with Service Bus: Cross-Platform Interoperability
Scenario 2: Manage Messaging Entities Across Clouds
The Tenant Experience
Subscriptions, Plans and Service Bus Namespaces
Visual Studio LightSwitch and Entity Framework 4.1+

<Return to section navigation list>
Cloud Security, Compliance and Governance

<Return to section navigation list>
Cloud Computing Events
Neil MacKenzie (@mknz) will present Apache Cassandra on Windows Azure to the San Francisco Bay Area Azure Developers group at Microsoft’s San Francisco office on 8/27/2013:
Apache Cassandra is a NoSQL database in which a distributed architecture supports high scale and availability on commodity hardware. It provides a model for understanding how to create scalable systems in the cloud. Cassandra is particularly useful for workloads requiring high write throughput, such as time-series data and logs. In this presentation, Neil Mackenzie will provide an introduction to Cassandra and describe how to use it in Windows Azure.
Neil Mackenzie is Windows Azure Lead for Satory Global, where he helps companies migrate onto the Windows Azure Platform. He has been using Windows Azure since its public preview at Microsoft’s Professional Developers Conference (PDC) 2008. Neil wrote the Microsoft Windows Azure Development Cookbook. He speaks frequently at user groups and in Windows Azure training sessions
Microsoft San Francisco (in Westfield Mall where Powell meets Market Street), 835 Market Street, Golden Gate Rooms - 7th Floor, San Francisco, CA (map)
We are in the same building as Westfield Mall, 7th Floor
<Return to section navigation list>
Other Cloud Computing Platforms and Services
Jeff Barr (@jeffbarr) reported Additional IP Address Flexibility in the Virtual Private Cloud in an 8/21/2013 post:
VPC So Far
The Amazon Virtual Private Cloud (VPC) lets you provision a logically isolated section of the AWS Cloud where you can launch AWS resources in a virtual network that you define. Earlier this year, in my post Virtual Private Clouds for Everyone, I outlined some important changes to Amazon EC2 which combine its ease of use with the advanced networking features of Amazon VPC.
As part of that launch, we introduced the concept of the default subnet for default VPCs. EC2 instances created in the default subnet automatically received public IP addresses; instances in the other subnets did not. This was a very sensible default behavior because it made the new VPC feature more or less transparent.
More Control
Today we are launching a new feature that gives you additional control of public IP addresses in VPC at launch time. Here's the scoop:
- When you launch an instance into a default subnet, you now have the ability to decide if the instance is given a public IP address. Until now, launches into a default subnet were always assigned a public IP address and there was no way to remove it.
- When you launch an instance into a nondefault subnet, you can now choose to assign a public IP address as part of the launch. In the past you had to launch the instance and then allocate and attach an Elastic IP address after the instance became available.
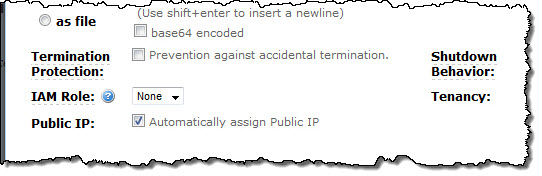
The AWS Management Console includes complete support for this new feature. If you are launching into a default VPC and you don't select a subnet, or if you are making a Spot Instance request, you can check or uncheck a single check box in the launch wizard to select the desired outcome:
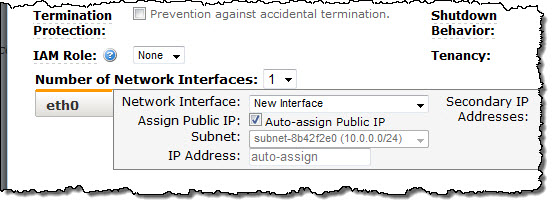
If you choose a specific subnet for your launch, you will see a similar checkbox in the ENI (Elastic Network Interface) section of the launch wizard:
The initial setting of the checkbox (checked or unchecked) reflects the behavior introduced when we launched VPCs for everyone. In other words, if you want the existing behavior, leave the checkbox the way you found it.
Some Notes
I should note that this feature is available only at launch time. If you do not assign a public IP address to an instance during the launch, you can associate an Elastic IP address after the instance has been launched.Also, if, for some reason, you decide to attach an Elastic IP address to an instance that already has a public IP address, the Elastic IP address will replace the public IP address. When you detach the Elastic IP address from the instance, a new public IP address will be assigned to the instance.
We expect to add CloudFormation and Auto Scaling support before too long.
To learn more about this new feature, read the Using Instance Addressing topic in the EC2 documentation.
No significant articles so far this week.
<Return to section navigation list>



































0 comments:
Post a Comment